At Telefónica, we are committed to technological innovation and service excellence as core pillars to build trust and support the digital development of individuals, companies, and public administrations.
Telefónica: leading telecommunications company
Communication Room
Know all the newsPress room
- 28/05/2026
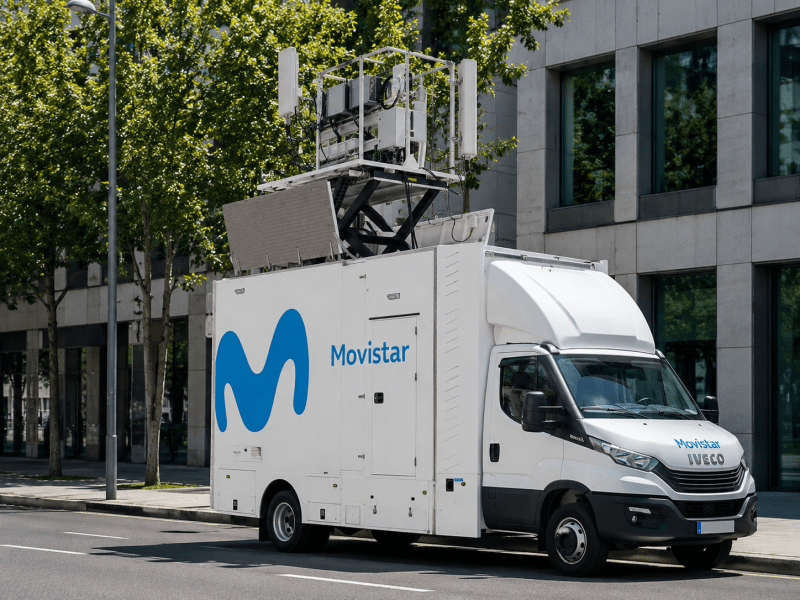
Telefónica is driving the development of more efficient networks and has reduced its energy consumption by 12% despite strong growth in data traffic
- 27/05/2026
Telefónica’s socio-economic impact amounts to 652,000 jobs and €45.4 billion in GDP across its main markets
- 19/05/2026
Telefónica successfully issues a €750 million bond
ESG
ESG
Deliver the best digital experience to all our customers by providing connectivity and advanced services tailored to their needs.
MissionTransform and Grow is a roadmap that connects Telefónica’s purpose with the opportunities of the digital future.
StrategyConnectivity is the first requirement to access the digital world. Networks are the most powerful transformative platform.
Networks and technologyConsumer trust and confidence in digital environments, safety and digital literacy, is vital for the digital economy.
Public Policy and Regulation
We have the ability to anticipate the future, understand the needs of the company and continue to be pioneers in the digital world.
InnovationEconomy
Shareholders & InvestorsCommunication room #Shareholders & Investors
- 14/05/2026Telefonica increases its revenue to €8,127 million in the first quarter and confirms its financial targets for 2026
- 26/03/2026Telefónica advances in its transformation to become “one of Europe’s leading telecommunications companies by 2030” after meeting its 2025 targets
- 24/02/2026Telefónica accelerates its growth in the last quarter of 2025 and increases revenues, adjusted EBITDA and free cash flow